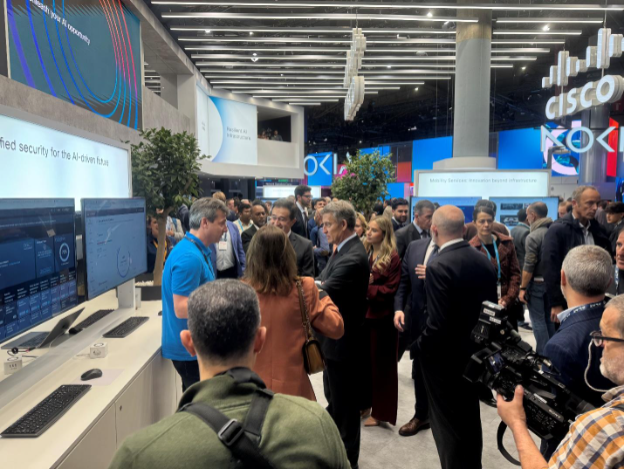
Cell World Congress 2025 in Barcelona delivered on each promise – a record-breaking occasion with 109,000 attendees from 205 international locations, with over 2,900 exhibitors, sponsors, and companions showcasing a formidable array of chopping‐edge matters, from 5G and IoT to Unified Safety for the AI-driven Future.
As all the time, Cisco’s presence showcased a collection of improvements, similar to the most recent safe connectivity options, demonstrated subsequent‐gen wi-fi improvements, and made a number of high-profile media bulletins that underscored our dedication to shaping the way forward for digital communications.
Cisco’s One Cisco technique was on full show, integrating networking, safety, observability, and Splunk options to ship unparalleled outcomes. This holistic strategy showcases how our clients can obtain AI-ready information facilities, future-proofed workplaces, and digital resilience.
Cisco at MWC 2025: A Powerhouse of Innovation
In true Cisco vogue, our sales space wasn’t only a house however relatively a hub of innovation and collaboration. Stay Demo Highlights included:
Classes From Earlier Occasions
Constructing on our experiences at Black Hat, NFL Tremendous Bowl, RSA Convention and others the Crew introduced the identical power and technical rigor to MWC 2025. Our SNOC staff leveraged the operational excellence honed at these occasions, mixing state-of-the-art safety instruments with real-time community monitoring to make sure seamless occasion operations.
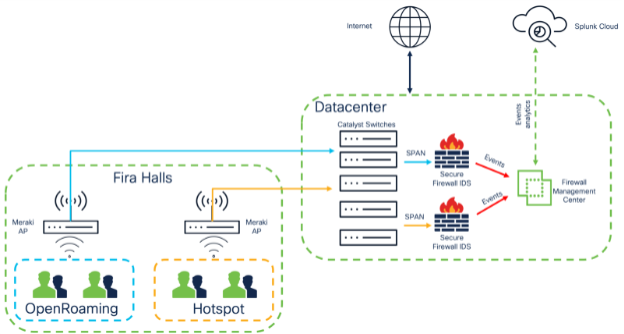
The Splunk Cloud was used as the information platform, including Apps for information ingestion:
With these integrations, our SOC staff was capable of construct a CISO stage SNOC dashboard for vital telemetry from all community and safety sources.
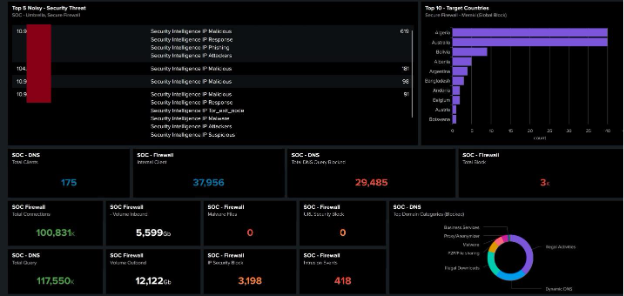
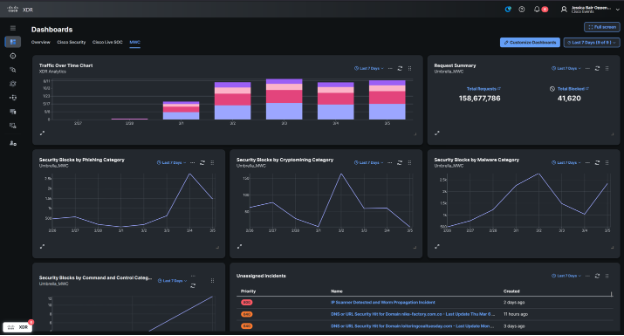
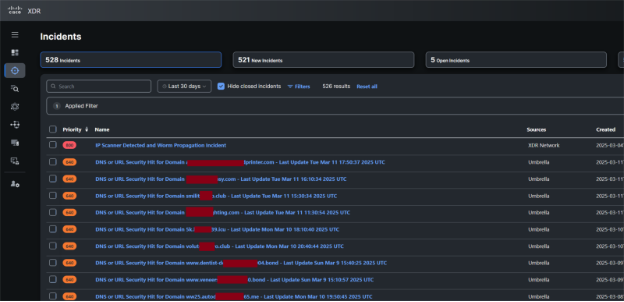
We additionally had SOC Supervisor stage dashboards for XDR Incidents, Firewall Occasions and DNS Safety.
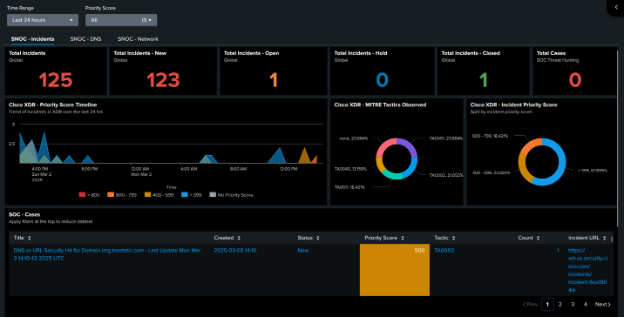
We additionally related the integrations with Cisco XDR, for Dashboard visibility and Incident investigation.
We had XDR Automate workflows to advertise menace detections in Splunk to XDR Incidents, and the XDR integration again into Splunk.
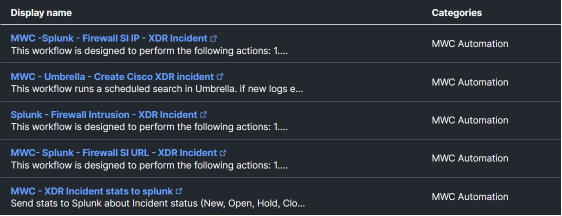
The Incidents empowered the SNOC staff to prioritize investigations.
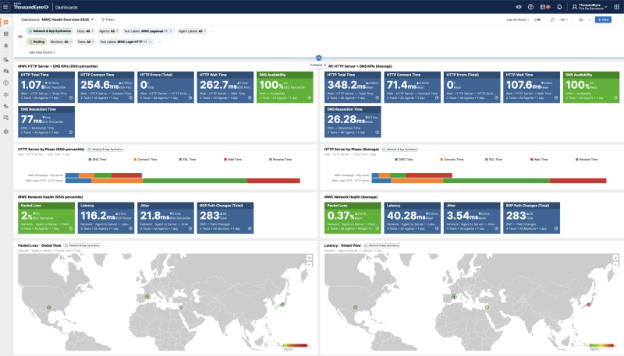
Moreover, at this yr’s Cell World Congress in Barcelona, Cisco’s ThousandEyes dashboard was instrumental in offering sturdy community assurance. Attendees benefited from real-time monitoring and insights into community efficiency, making certain a seamless expertise from begin to end. With the aptitude to trace vital elements just like the occasion homepage and login processes, ThousandEyes ensured that individuals might entry important assets swiftly and with out interruption. This stage of detailed visibility and management helped preserve the integrity and reliability of the community all through the occasion.
Day 1: A Check of Scale
Day 1 was all about dealing with large community exercise seamlessly. From just a few employees gadgets to 1000’s of gadgets connecting concurrently, our firewall and community monitoring techniques carried out flawlessly, processing a excessive quantity of visitors whereas sustaining pinpoint visibility. The sturdy efficiency of our Cisco safety options reaffirmed that, whether or not in a managed lab atmosphere or amidst a vibrant convention, community resilience is just not negotiable.
Day 2: When a Russian Menace Tried to Crash the Occasion
Simply as you suppose the one surprises at MWC 2025 are the progressive tech and spontaneous demos, our firewall logs gave us an surprising twist. On Day 2, our vigilant monitoring detected an anomalous occasion: a privilege escalation occasion coming from a Russian supply.
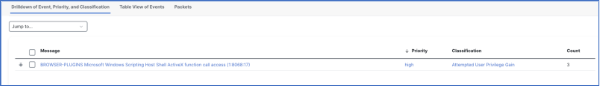
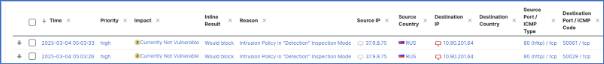
Our technical maestro, Jorge Quintero, instantly flagged this as a possible high-risk occasion – a state of affairs the place an endpoint is likely to be compromised. The logs confirmed a sample in keeping with C2 communications, prompting a speedy investigation and swift remediation measures. In true SNOC fashion, we ensured that any unwelcome visitor was proven the door earlier than it might wreak havoc. (It appears even at MWC, cyber adversaries can’t resist the attract of the celebration!)
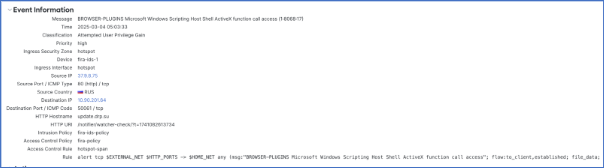
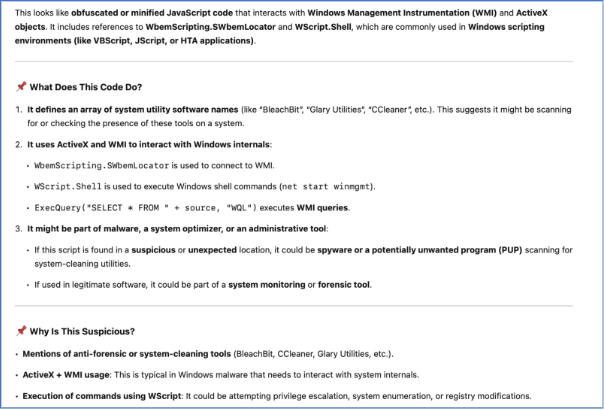
What actually stood out on this IDS occasion was a crafted plain-text script operating on port 80 with Web Explorer (sure – nonetheless in use).
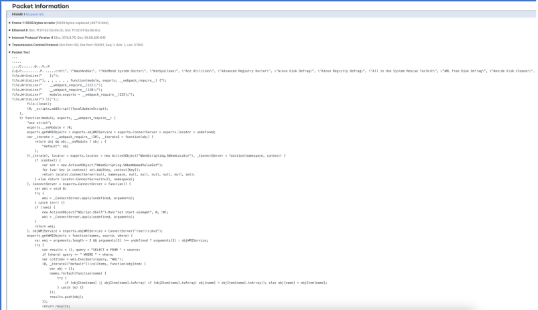
The Snort signature that was triggered additionally highlighted two most important methods getting used:
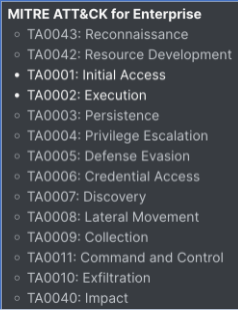
Utilizing public generative AI instruments, the evaluation of the payload yielded the next outcomes, revealing constant patterns of malicious exercise — together with makes an attempt to determine anti-malware instruments (seemingly for elimination to take care of persistence) and doubtlessly escalate privileges additional.
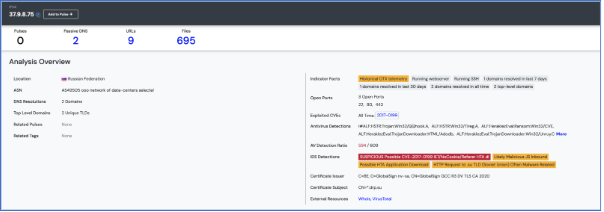
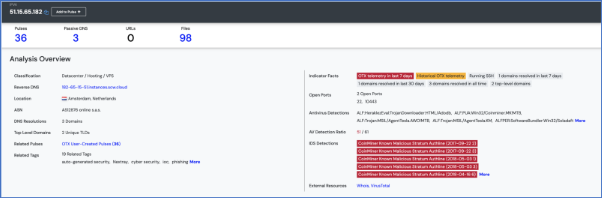
Lastly, what confirmed our suspicions (in the event that they weren’t already) got here from Talos and AlienVault menace intelligence. This IP deal with (belonging to the Russian Federation) had already been flagged for malicious exercise.
Day 3: Cryptomining — The Story of the Good and the Evil
Day 3 introduced an fascinating matter to our consideration — cryptomining. From its humble beginnings to the multi-billion-dollar business, it’s as we speak, we now have witnessed the rise of crypto — now extending past simply cryptocurrency to progressive makes use of within the fintech house, together with NFTs and extra.
Nevertheless, we now have additionally seen how this know-how has been leveraged by malicious actors, particularly to compromise endpoints and hijack computing assets for cryptomining.


Utilizing public generative AI instruments to decode plain textual content, we recognized mining software program (XMRig) making RPC calls to the Monero cryptocurrency community. Now, it’s value highlighting that, though suspicious, this might nonetheless be a authentic case of an endpoint operating mining software program.
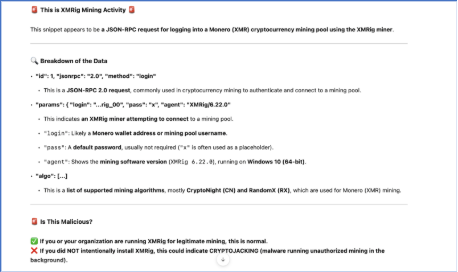
Nevertheless, the illegitimate nature of this exercise was confirmed once more by means of Talos and AlienVault intelligence. The general public IP deal with in use had already been flagged for involvement in malicious cryptomining operations.
Day 4: Slowdown and Occasion Wrap-Up!
Day 4 confirmed a slowdown in exercise, making it a threat-free day and giving us time to research and combination all the dataset from the occasion. Listed below are a few key takeaways from the firewall evaluation:
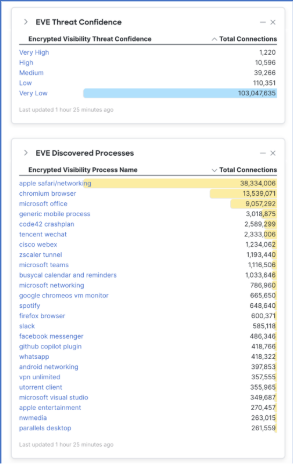
1. EVE (Encrypted Visibility Engine): Paving the way in which for encrypted visitors evaluation.
Cisco’s Encrypted Visibility Engine (EVE) has confirmed that the innovation of current years is critical. Monitoring at Fira was performed completely utilizing IDS (Intrusion Detection System) with passive evaluation. Even with out decryption capabilities, we have been capable of determine threats inside encrypted visitors, in addition to the processes producing these visitors stream.
2. Occasion-driven analytics, powered by Splunk
The Cisco + Splunk story is a match made in heaven. With Cisco’s depth and breadth in safety and a powerful portfolio, mixed with Splunk’s world-class observability and suppleness, we have been capable of construct highly effective, actionable dashboards for simple consumption by the SNOC staff.
Beneath is the aggregated information for all the occasion — protecting the whole lot from connection occasions, file occasions, and intrusion occasions to a prioritized set of incidents recognized all through the conference.
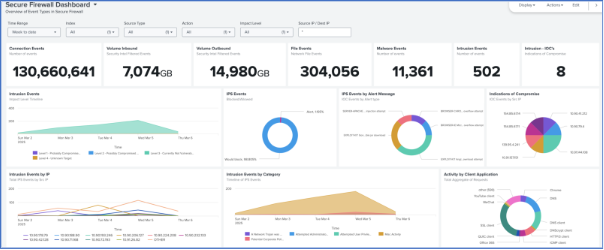
This included DNS safety blocks, defending Fira’s Community attendees at MWC, from malicious web sites. Over 14,400 apps have been seen on the MWC community.

Trying Forward
The surprising incident on Day 2 solely strengthened one very important lesson: in as we speak’s hyper-connected world, innovation should all the time be matched with rigorous safety. As we replicate on the successes of MWC 2025, we’re already planning enhancements to our menace detection and incident response capabilities, drawing on each our MWC, Black Hat, and NFL experiences.
Cisco’s SNOC Crew stays dedicated to staying one step forward, turning each problem into a possibility to innovate and defend. Whether or not it’s managing tens of 1000’s of connections or intercepting a rogue C2 sign, we’re prepared to make sure that the digital future is as safe as it’s good.
Whereas know-how was on full show, the true stars of the Safety Sales space have been the devoted people who introduced these demos and operations to life. A heartfelt thanks to: Alberto Torralba, Filipe Lopes, Jorge Quintero, Jervis Hui, Nirav Shah, John Cardani-Trollinger, and Emile Antone. Their experience and dedication ensured that each demo ran flawlessly and captured the eye of each attendee. Particular appreciation to Ivan Padilla Ojeda, who was our liaison with the community staff to attach the whole lot within the SNOC.
Additionally, thanks to those that helped us put together for the SNOC: Ivan Berlinson, Ryan Maclennan, Aditya Sankar, Seyed Khadem, Tony Iacobelli, Dallas Williams, Nicholas Carrieri and Jessica Oppenheimer.
Wrapping Up
Cell World Congress 2025 was not nearly showcasing the following wave of technological innovation; it was additionally a robust demonstration of how built-in, resilient safety measures can safeguard even essentially the most bustling, high-stakes environments. The comparative insights from Day 1 and Day 2 underscore the significance of staying one step forward, always adapting, and constantly enhancing our protection methods.

Thanks for becoming a member of us on this journey by means of MWC 2025 and keep tuned for extra insights and behind-the-scenes tales from MWC 2025. In spite of everything, on the planet of tech, it’s by no means simply one other day on the workplace!
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share:


